About Us
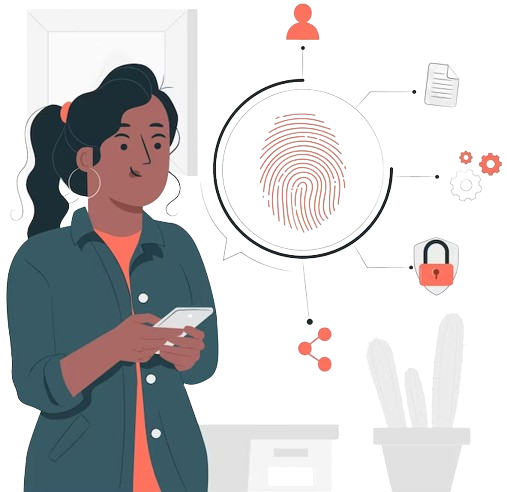
Heritage Cyber World: Center of excellence for Uphold your business security and turn down all the cyberattacks.
Heritage Cyber World is where all the cyber attacks and vulnerabilities lose the bet. We are a dedicated team or, you can say, a hub where we prioritize business security, putting all other things secondary. The hub where DRONA, the command center, takes into play to deliver a 24/7 integrated approach to security. At our dedicated center, we have a security specialist who takes out cyber threats from the picture. At Heritage Cyber World, we have always been on the road to spreading advanced-level security where businesses enjoy making deals, and we power the roots of security. With our service line from cybersecurity, digital forensic service, and dark web monitoring, we lead the way in security. We have several services and solutions in our capture with the prime move towards ending the space for cyber attacks. Count on to defeat every cyberattack that gets on to business.